CISA Warns of Active Exploitation of Trimble Cityworks Vulnerability. The organization has issued an urgent warning regarding an exploited security flaw in Trimble Cityworks. Cityworks is designed to assist local governments and utility agencies in a multitude of areas. These include management of capital assets, workflows, communication, licensing, and permits. The cloud-based platform enables users […]
Blog
CISA and FDA are Warning of Critical Medical Vulnerabilities
CISA and the FDA are Warning of Critical Medical Vulnerabilities. The U.S. Cybersecurity and Infrastructure Security Agency (CISA) and the Food and Drug Administration (FDA) are issuing alerts about the presence of hidden functionality. This hidden functionality can be found in Contec CMS8000 patient monitors and Epsimed MN-120 patient monitors. The vulnerability makes these monitors vectors […]
Third-Party Apps are Accessing User Data Without Permission
Third-Party apps are accessing user data without permission. New research from web exposure management specialist Reflectiz highlights alarming website vulnerabilities across industries. Using proprietary data from the top 100 websites by traffic in each sector, the findings reveal critical risks: 45% of third-party apps access user data without proper authorization. 53% of retail risk exposures […]
Smartphones can leave your organization open to vulnerabilities
Smartphones can leave your organization open to vulnerabilities. Cybersecurity researchers have uncovered a critical vulnerability in the Monkey’s Audio (APE) decoder on Samsung smartphones. This potentially allows attackers to execute malicious code. This high-severity flaw affects Samsung devices running Android 12, 13, and 14, according to a December 2024 advisory from Samsung. The Danger this […]
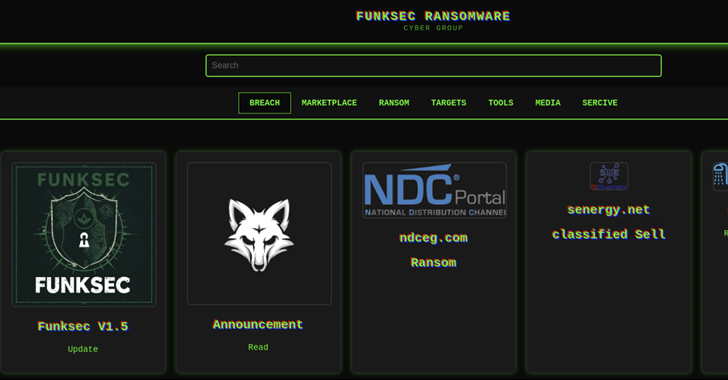
Ransomware is Utilizing AI for Extortion and Data Brokering
Ransomware is Utilizing AI for Extortion and Data Brokering. Cybersecurity researchers have uncovered an AI-assisted ransomware group, FunkSec, that emerged in late 2024. According to Check Point Research, FunkSec employs double extortion tactics, combining data theft and encryption to pressure victims into paying unusually low ransoms—sometimes as little as $10,000. The group also acts as […]
Malware is putting financial instiutions in jeopardy
Malware is putting financial institutions in jeopardy. Brazilian banking institutions are under attack from a custom variant of the AllaKore remote access trojan (RAT), dubbed AllaSenha, according to French cybersecurity firm HarfangLab. The malware, designed to steal banking credentials, uses Azure cloud infrastructure for its command-and-control (C2) operations. Targeted banks include Banco do Brasil, Bradesco, […]
Electrical utility enterprises are increasingly vulnerable
Electrical utility enterprises are increasingly vulnerable. The U.S. Cybersecurity and Infrastructure Security Agency (CISA) has issued a critical advisory regarding multiple vulnerabilities affecting Schneider Electric’s Easergy medium voltage protection relays. According to CISA, successful exploitation of these vulnerabilities could lead to serious consequences, including: Exposure of device credentials Denial-of-service conditions Unexpected device reboots Full attacker […]
Hackers are targeting construction firms
Hackers are targeting construction firms. The construction industry is facing growing threats from cyberattacks, with hackers specifically targeting FOUNDATION Accounting Software. Sub-industries such as plumbing, HVAC (heating, ventilation, and air conditioning), and concrete are among those being affected. “Attackers have been observed brute-forcing the software at scale and gaining access simply by using the […]
Malware targets law firms in widespread cyberattacks.
Malware targets law firms in widespread cyberattacks. A key player in these attacks is GootLoader, a stealthy malware. Craftily, it works by gaining access to systems and delivering ransomware or other harmful payloads. GootLoader typically uses search engine poisoning, manipulating results to direct users to compromised WordPress websites where the malware is downloaded. History of […]
Why is Healthcare a Prime Target in Cyber Attacks
Why is Healthcare a prime target in cyber-attacks? Imagine an attack that halts emergency rooms, delays surgeries, or exposes private health data for extortion. This is the reality as cybercriminals target healthcare systems, exploiting the people who rely on them. Since 20121, healthcare has accounts for 17.8% of all breaches and 18.2% of ransomware attacks, […]